The Key to An Effective Data Resilience Strategy
The need for data resilience planning has never been more critical. Organizations must protect against and recover quickly from data-destructive events ranging from cyberattacks to natural disasters to system failures to human error. Every business is unique, so determining your storage security needs starts with understanding what infrastructure and tools you currently have, and defining what objectives you are trying to accomplish.
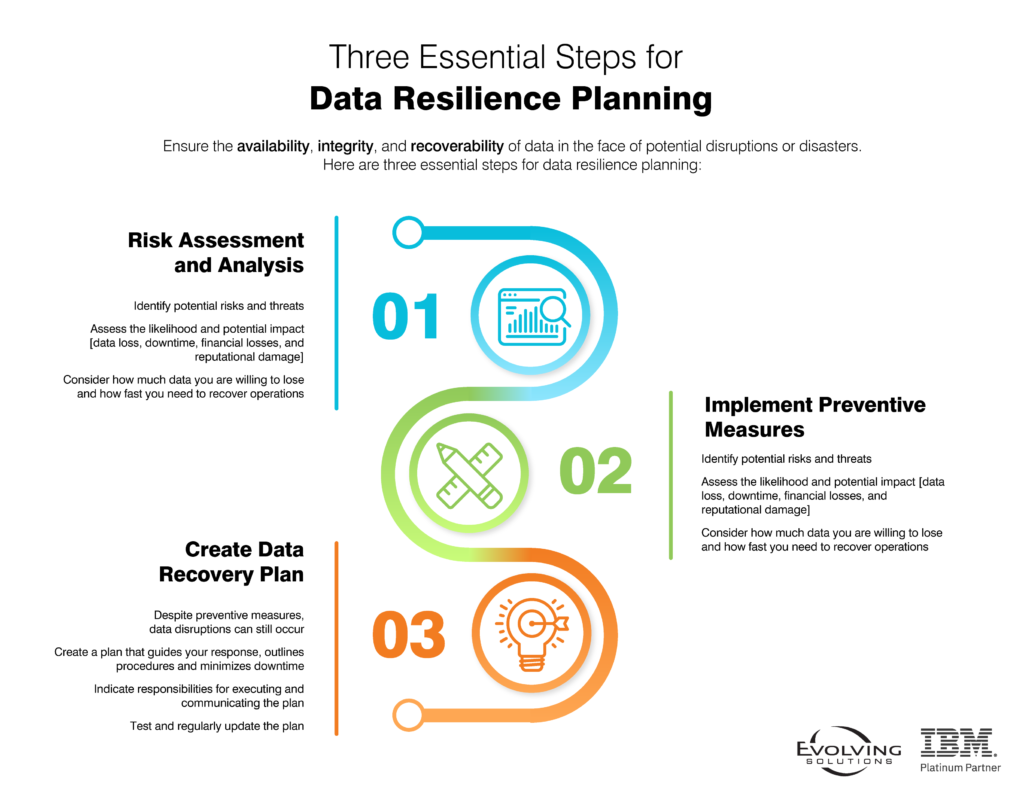
As organizations begin data resilience planning, they should ask themselves:
- How much data are you willing to lose?
- How fast do you need to recover your operations?
The answers to these two questions can help narrow the options and provide a starting point that can lead to a well-planned data resilience strategy.
How Much Data Resilience Is Enough?
Careful planning and organization-wide collaboration are essential. IT and corporate leaders are ultimately making an intuitive determination about data resilience, asking themselves “how much is enough?”
The answer to this question differs for every organization. The degree of data protection measures required varies greatly by industry. The highest levels of data protection are typically found in the financial world, where the impact of system downtime and/or lost records can be easily quantified. In addition, financial institutions operate under strict industry and governmental regulations for protecting customer and client data.
However, not every business requires continuous availability. For example, a manufacturing site that is knocked offline by severe weather may be able to endure 24 hours or more without systems access.
So as an initial step, organizations should determine a recovery point objective (RPO). The RPO defines how much data an organization can afford to lose. The RPO coupled with the recovery time objective (RTO), which outlines how long an organization can survive without data access, serve as data resilience guideposts for companies.
Many organizations stop after making a data resilience plan. However, actually practicing a recovery scenario is an important, and often overlooked, component of data resilience. Many businesses use IBM Safeguarded Copy to protect against threats, but they do not practice recovery or spend time analyzing copies of data to determine that they are good and clean. Without the additional step of data validation, these organizations have an incomplete solution.
As an example, Evolving Solutions has a client that regularly switches production workloads between data centers. The result is that the organization does not have to test its disaster recovery capabilities in the same way because they perform the required tasks on a regular basis. Many other clients have a data resilience plan, but they have not tested their failover strategies. We recommend testing and practice to ensure the planning works.
A key part of site switching lies in automation. While IBM has built automation into many of its solutions including IBM Safeguarded Copy, GDPS, PowerHA, database tools, application toolsets, and others, some of the onus is on the user. An organization can automate the creation of these safeguarded copies for ransomware protection and automate their restore of them into a forensic environment, but it is the organization’s responsibility to use the database tools, the application toolsets or some other method to examine that copy and validate the data it contains. If the data in the copy is bad, the organization must keep going back in time to older copies to find the preferred restore point.
An Outline of IBM Storage Solutions for Data Resilience
IBM Storage provides several solutions that promote data resilience:
- IBM FlashSystem: Per the name, this family of enterprise storage systems stores data on flash memory chips rather than traditional solid-state drives. Each model is based on a common storage software platform and utilizes a single user interface for centralized management of virtual, container, and hybrid cloud storage environments. These systems feature support for NVMe and can utilize IBM FlashCore-enhanced storage media that provides significant flash density and storage capacity.
- IBM DS8000 series: IBM’s pinnacle of block storage performance and reliability for both open systems and mainframe workloads, the DS8000 family delivers ultra-high levels of data resiliency, support for complex 4-site+ replication configurations, and the unique capability to replicate data around the world with a sub 5-second RPO.
- IBM tape storage: With the escalating sophistication of cybercrimes, organizations are showing renewed interest in tape storage solutions. IBM’s LTO tape drives and TS1160 and TS1150 models feature air-gapped technology, while the Diamondback and TS4500 and TS4300 tape libraries are well-suited for cloud environments.
- IBM Safeguarded Copy: IBM Safeguarded Copy allows users to create granular, immutable protected point-in time copies of active production data that cannot be altered or deleted. The solution leverages existing Copy Management software for testing and ease of recovery of copies.
- IBM Cyber Vault: An automation and security blueprint built on top of IBM Safeguarded Copy, Cyber Vault analyzes copies of data in search of potentially malicious changes that could indicate the presence of ransomware, allowing admins to quickly identify, test, and restore from good copies.
Determining which solution or solutions to implement begins with careful planning of an organization’s complete architecture. Evolving Solutions recently worked with a client that wanted a ransomware protection solution. The organization was interested in implementing IBM Safeguarded Copy. Based on our familiarity with and knowledge of the client’s IT environment, we advised them to first consider their storage environment as a whole: the network, the server platform, the application. While Safeguarded Copy is an important and unique offering in cyber resiliency, it is only part of the puzzle and is in fact among the final pieces. Instead, we reviewed the organization’s complete architecture, which provided a path to security, involving thorough investigation and careful planning.
Understanding Data Resilience Business Requirements
Because every environment is unique, determining organizational data resilience strategy needs, including the area of storage security, starts with understanding your business requirements and identifying what you are trying to accomplish. IT must be able to protect against and recover quickly from data-destructive events ranging from cyberattacks, natural disasters, system failures, and human error.
Let’s Talk. To learn more and determine if you have the right data resilience strategy, you can schedule time to talk with our technical experts. We have over 25 years of experience defining IBM Storage strategies and guiding clients with data resilience planning.